Charles Guebels
IaC and diagram generation with Former2

Former2 is a web-based tool capable of generating Infrastructure as Code (IaC) templates and cloud architecture diagrams for the AWS cloud. In this article we will mainly present these two features.
Setup
For both IaC templates and diagram generation, the mechanism is the same, Former2 must be configured to use an access key and a secret access key able to access an AWS account. Once configured, Former2 will use the JavaScript SDK to scan the account and retrieve the configuration of each AWS resources.
IAM permission
The first step is to create an access key and a secret access key. One possible way to do that is to follow the instructions below:
- Open the AWS IAM service;
- Open the “Users” section and click on the “Create user” button;
- Give a name to the new user, for example “former2”, do not check the checkbox to give console access and click on the “Next” button;
- On the next page, select “Attach policies directly” and search for the AWS read-only managed policy named “ReadOnlyAccess”. To ease the search, filter by “AWS managed - job function” policy type. Once found, select the policy and click the “Next” button;
- On the next page, just click on the “Create user” button;
- The page with the list of users appears, click on the “former2” user and open the “Security credentials” tab;
- In the “Access keys” section, click on the “Create access key” button;
- In the “Access key best practices & alternatives” page, select “Third-party service”, check the confirmation checkbox at the bottom of the page and click on the “Next” button;
- In the next page click on the “Create access key” button;
- Preciously note the generated access key and the secret access key or download the CSV file.
Former2 setup
Once the access key created, we can start to configure Former2:
- Open https://former2.com/#section-setup-credentials.
- Enter the access key and the secret access in the first two fields and click somewhere outside the form, this click will trigger the authentication. If it works, the text “Logged in as:USERNAME @ ACCOUNT_ID” will appear;
- Click on the “Continue to Parameters” button;
- Enter some custom CloudFormation stack parameters if needed and click on the “Continue to Settings” button;
- We reach the “Settings” page, it is the last setup one. In this page you have several parameters about, for example, how the CloudFormation code will be formatted. In our case we can let the default settings.
It is important to know that Former2 uses the JavaScript SDK to scan the AWS accounts and that for some services it is not possible due to the CORS restriction. To get around this restriction, Former2 offers a browser plugin that we can download on this page. The list of services which require the browser is available here.
Triggering the account scan
Before triggering a scan account, we have to check that the region specified at the top right of the page is correct. The selected region must be the AWS region where we want to scan the resources.
Once everything is configured correctly, we can click on the “Scan Account” green button at the top right. This scan takes a few seconds.
Resources selection
Now that the scan is done, it’s’ time to select the resources for which we want to generate the IaC template or the diagram.
To do this, simply browse the different services available in the menu on the left. For each desired resource category page, select the desired resources and click the “Add Selected” blue button. This will increase the total number of selected resources next to the “Generate” blue button at the top left of the website.
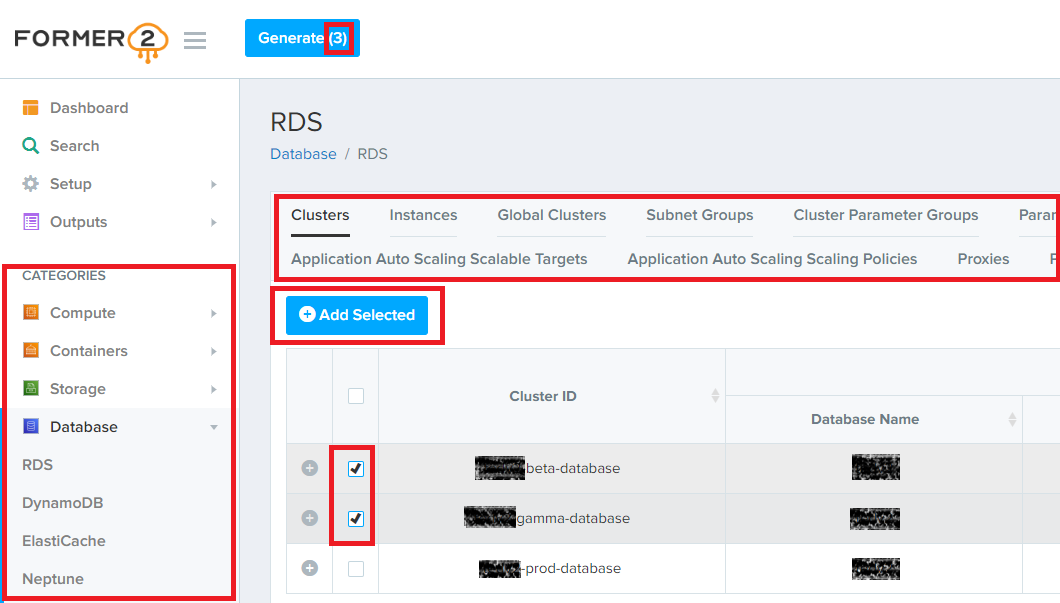
For information, in the “Setup / Settings page” there is an experimental feature to add all the resources at once.
IaC templates and diagram generation
Once all the desired resources have been selected, we can click on the “Generate” blue button at the top left of the website. After a very short delay, Former2 automatically opens the “Outputs” menu on the left and displays, by default, the CloudFormation generated template.
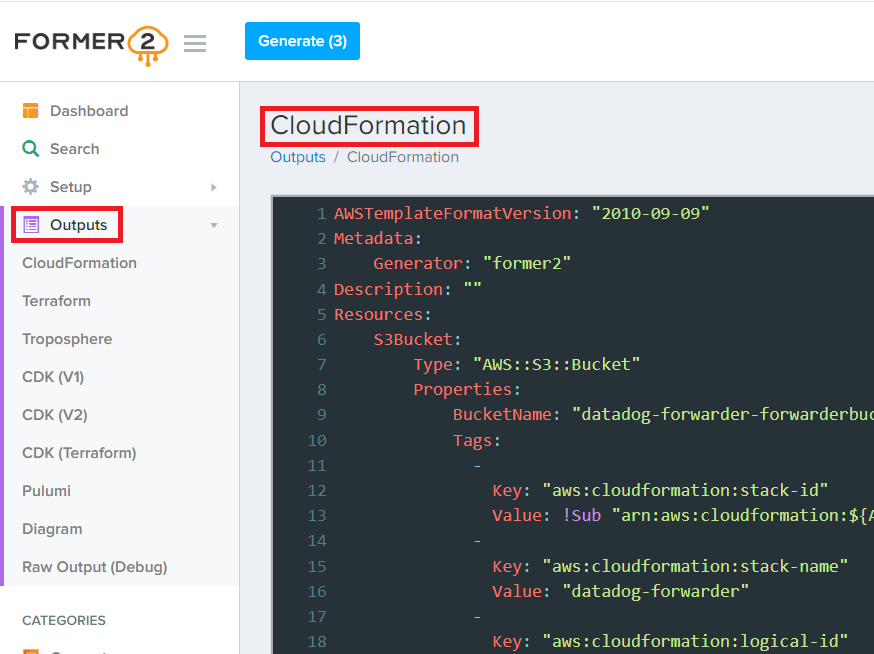
We can see that Former2 is also able to generate IaC templates in other formats:
- Terraform;
- Troposphere;
- CDK V1 and V2 (Beta);
- CDK Terraform (Beta);
- Pulumi (Beta).
The additional interesting feature is that Former2 is also able to generate an editable DrawIO diagram with the selected resources.
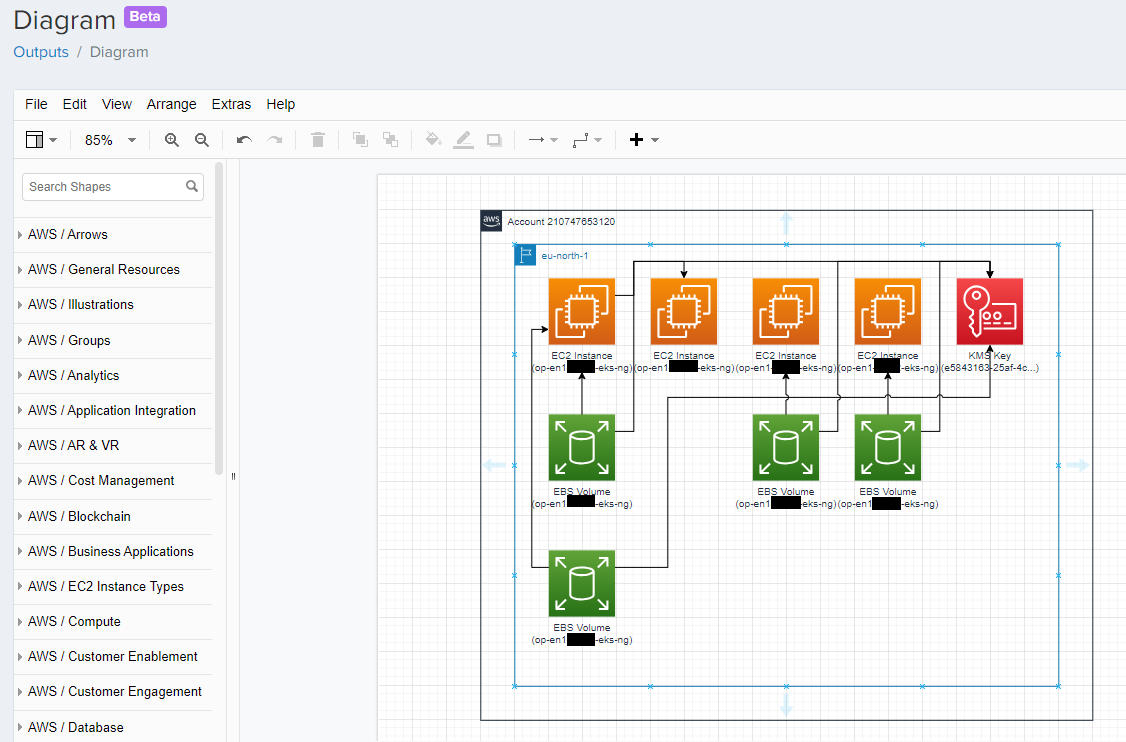
Unfortunately, the generated diagram is often not really readable without modifications, but at least the correct boxes are already created with the correct service icons and names.
Importing resources
Former2 also allows us to create AWS resources directly from a CloudFormation template that we can import. It is important to note two things about this:
- This only works for CloudFormation;
- The IAM policy assigned to the access keys must be updated to allow the creation of relevant resources. The policy must also have appropriate CloudFormation permissions to create CloudFormation resources like Stack, ChangeSet etc.
To import a CloudFormation template, simply open the “Outputs / CloudFormation page” and click on the “Import” button. A new page will be displayed where it will be possible to select the Stack Name and the Deletion Policy.
Former2 limitations
Some limitations can be attributed to Former2:
- Once selected we cannot deselect the resources. It is necessary to reset the entire selection and restart the selection;
- No real documentation;
- Many features in experimental and beta version;
- The IaC templates are generated without file structure or parameters, only a single big file is generated with all the attributes hardcoded;
- The generated diagrams require numerous adjustments to be really readable (feature still in Beta);
- The manual diagram updates are reset each time a new generation is triggered;
- It is not possible to generate a diagram based on a imported CloudFormation template without creating a CloudFormation stack.
Conclusion
The Former2 tool appears to be in its early stages as many features are still in beta. The IaC templates generation is useful to dump an AWS account configuration but not really to include it in a production project. The generated code is neither structured nor parameterized.
Diagrams generated with Former2 are difficult to read when only a few resources are selected. The diagrams are editable but unfortunately the modifications must be redone each time a new generation is triggered.
Let’s follow this project to see how it will evolve.
